tl;dr
- Chrome history analysis
- ACE file analysis
- Detecting the virus
Description
I could not solve this challenge at the time of the CTF. But it is a nice challenge.
Given with an Windows 7 memory dump, lets see what all processes are running in the machine/system.
Initial Analysis
As the description of the says that the operator was browsing web the he might be using one of the browsers like Chrome, Firefox, or inbuilt Explorer. So lets go and see the pslist.
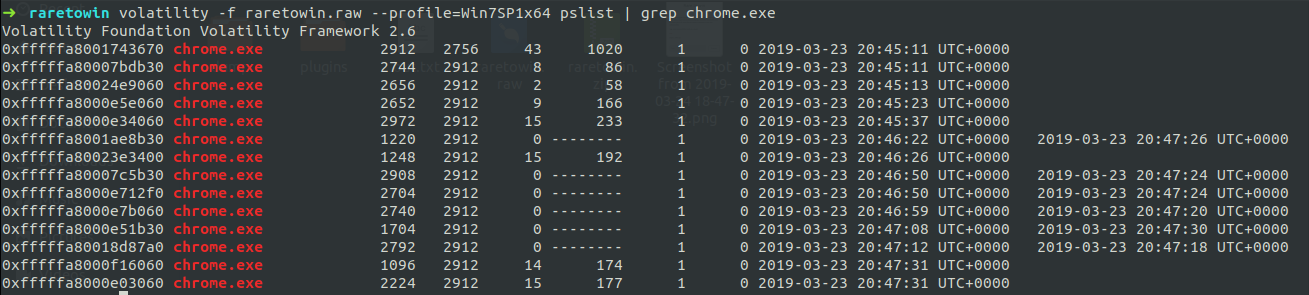
As we can see that chrome was running in system at the time when the dump was captured. So as the Chrome was running in the system we can use chrome history plugin and get the users history data.
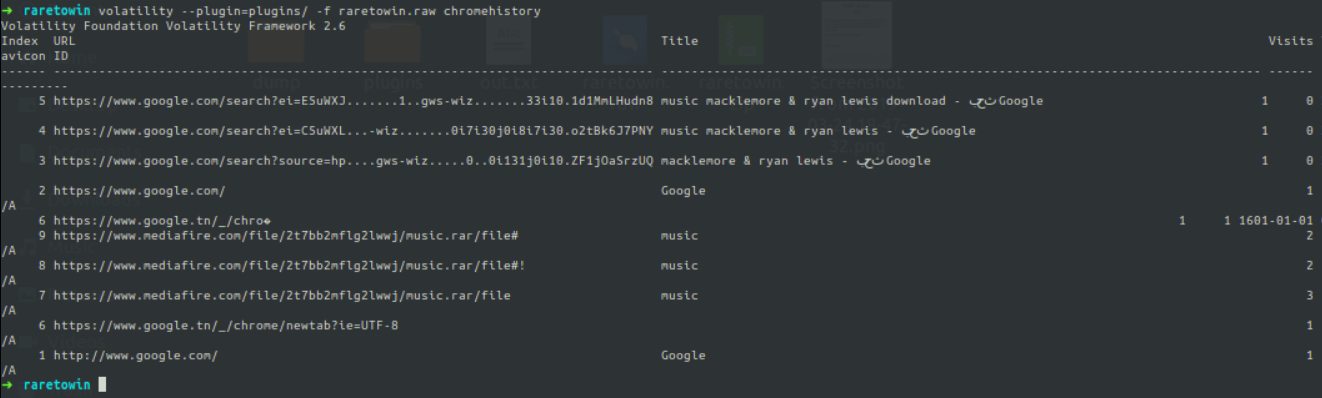
Further Analysis
As we can see that, there is file called music.rar was downloaded from the chrome. So we will search for the file in the dump, using filescan plugin.
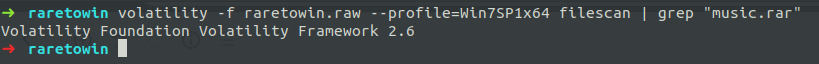
It resulted that there is no file relating to it. So I have downloaded the file from the link he browsed.
I tried opening the rar but it does not shown any files and it was in Read Only mode. So tried running file command on it and got to know that it is an ACE file.
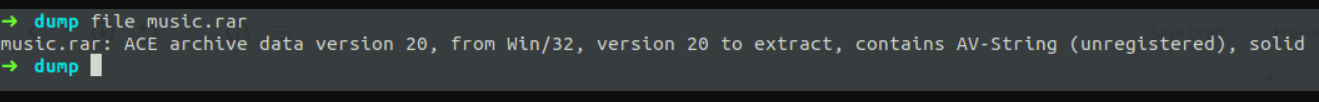
After a quick search in google, i came to know that there are some tools to open and extract the file from the ace file. So I renamed it and tried the unace command line tool which was provided by the Ubuntu software. But it doesn’t gave any results. So I checked for other alternatives and found this.
After using that tool, I can see that there is a firefox.exe and it is unable to override the build in firefox of the host system as I didn’t run with sudo permission.
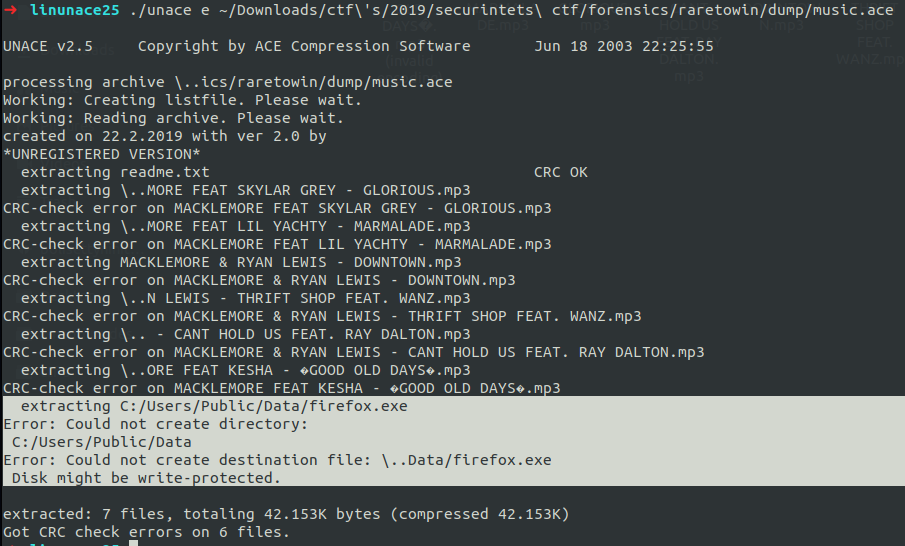
And also if we use binwalk on the that ace file, we can see an ELF file present in it. And loading that in gdb and seeing the main function of the elf, there is only one operation going on that is the printf function. So we can say that the exe was the virus that the challenge author has asked.
Flag
But the flag is the path_to_the_virus. So as we can see that the exe file was extracting to C:/Users/Public/Data/firefox.exe therefore that will be the path that they have asked.
But in windows the folders are divided using “\\” so the resulting path is C:\\Users\\Public\\Data\\firefox.exe.
And the flag will be,
Flag : securinets{84117b4eb400242a9db464e84220e672}
If you liked my solution, please do share it. I’m available on Twitter: @NihithNihi